How can I tell if my website has been hacked?
For most people, the first time they know their site has been hacked is when their web browser blocks them from visiting the site. So, how can I tell if my website has been hacked? The problem is most people don’t visit their own site very often, so it could have been in that state for weeks or even months. At this point it’s disastrous, because it means your site has been infected for long enough for it to be reported and verified by 3rd parties and may even lead to your web hosting company from taking the site down.
From personal experience I can tell you that the feeling you get when you realise your site or server has been hacked is awful. It feels like all the blood has drained from your body and you’ve gone into shock.
Don’t panic
Some hackers will demand a ransom to restore your site. Never, ever pay a ransom. Chances are that they will not do as promised and you are then out of pocket by however many bitcoins they’ve demanded.
If you have a half-decent web hosting service they should have a recent backup of your site. So, the worst case scenario is that you’ll have to revert to the backup copy, and then re-do whatever changes you made since the backup.
So how can you tell your site is being or has been hacked?
Beside the obvious I’ve outlined above, there are many other reactive mechanisms which will alert you if your site has been hacked.
Even the best system administrators can’t monitor sites 100% of the time, and an attack can literally come at any time of the day or night. There are alerting mechanisms they can use, but by the very nature of most of them, they can only alert you after the hacking event has already taken place.
Your browser (Google Chrome, Mozilla Firefox or Microsoft Edge) or some plugin like Norton Safe Web will alert you if they detect malware, phishing or other strange behaviour on a site. However, it’s unlikely that you visit your own website very often so you may not see that. More likely is that one of your customers or site visitors will see the issue long before you do, after all they are the reason you have a website in the first place.
Checking for modified code
The best way to ensure that your site is as it should be is to use an on-site source code scanner which can verify the source files have not been tampered with. Some of these are done at an operating system level, and others can be run from a plug-in. In my experience the plug-ins can miss some alterations, but the operating system level scanners or command-line scanners are reliable.
On-site source code scanners
These are some really great tools you can use to tell if your website has been hacked, or is in the process of being hacked. Many hacks can take a long time to implement. They rely on a step-by-step process of identifying and exploiting vulnerabilities, until the full hack is in place. One of the best ways to prevent this is to use an on-site source code scanner. These tools will alert you if code is being changed. Then, you can plug the hole and nip the hack in the bud before it becomes a major issue.
Tripwire
Although it’s really old technology, Tripwire is designed to catch hackers trying to break into old UNIX servers by changing password files or uploading back-doors. However, in the world of websites it’s been given a new mission.
Tripwire creates signatures of the files on your filesystem when you tell it to (ideally just after you install them, but before the site goes live). It then constantly monitors the content of your site, and if anything is changed it sends an email to the configured admin user to alert them of the change.
WordPress CLI
WordPress CLI (Command Line Interface) uses signatures stored in .json files to verify the files on your website have not been tampered with. It also identifies missing files and files that have been added. It can be used to check both the WordPress Core and Plugins for alterations. The downside is that you have to run it from the command-line on the server, which means for many hosting accounts it just won’t be available to you. We use this as part of our regular routine in our WordPress Site Care service.
If you do have SSH access to the command line on your web server, then the following two commands are the most useful.
sudo -u username wp core verify-checksums
sudo -u username wp plugin verify-checksums --all
Wordfence
Possibly the most popular security plugin for WordPress is Wordfence. We don’t use it currently, but it does come highly recommended by others.
Sucuri Security
The next most popular security plugin for WordPress is probably Sucuri Security, we use it on all our sites and recommend it. It’s fairly effective and has some easy to implement features that will harden your site against all but the most determined hackers.
Off-site monitoring
We use a monitoring service on our websites that immediately alerts us to any downtime. Also, it sends an email to our support ticketing system and automatically elevates the ticket status to urgent. At the same time a support group and engineer is assigned and alerted.
Some off-site services even includes a scanning mechanism that tells you if a page has been changed more than a certain percentage. Many web pages don’t change at all or may only have a minor change like a date or copyright year. We monitor these pages and are alerted if more than a very small percentage of the page changes.
WebsitePulse and Pingdom provide services that include content monitoring. However, these are generally paid services, but they can be an effective way to get alerted in minutes if your site has been attacked.
Most good services include the ability to monitor from multiple locations. This is important because a hacked site does not always serve malware. Often, they only target users based on their location, the time of day, traffic source or other parameters. Monitoring your site pages from multiple locations can improve detection rates. However, these mechanisms will never be as good as an on-site scanner such as Tripwire.
Off-site scans
There are several services available that you can use to scan your site for malware and blocking.
- https://transparencyreport.google.com/safe-browsing/search
- https://www.spamhaus.org/lookup/
- https://www.virustotal.com/gui/home/url
- https://aw-snap.info/file-viewer/
- https://sitecheck.sucuri.net/
Reading log files
If your site is hacked you will certainly want to obtain the log files for the period since your site was clean until some time after the hack. Those log files will help to identify where the hack has originated from (usually another hacked server) so can at least block it in your firewall. The log files will also help to identify the vulnerability that allowed the hacker to break in.
If you are so inclined you can also manually read through your server logs, both the access logs and the error logs. They will certainly show a lot of attempted hacks, sometimes it’s a good idea to check if any of the more determined attempts have had any success.
Finding SQL injections
With the nature of dynamic websites it can be extremely difficult to identify SQL injections. Often they will just look like regular inserts and updates that you would expect to see. What you need to look for are inserts and updates that look unusual. If you have query logging turned on this can be useful as an injection will stand out like a sore thumb.
Sometimes it is easier to identify if someone is attempting to perform an injection than it is to find the injection itself. So, searching for authentication failures, and other denied events can often yield better results. However, there will be a lot of these, so you need to pair them with a successful event from the same address or user.
Locating added files
For WordPress this can be done easily using the WordPress CLI. For other sites you may been to be more pro-active and create manifest files of your website, or use a source code version control system such as Git. If you’re using Git then you can easily identify changes and additions to your site, and roll them back too.
Pay attention to your analytics and look for spikes
If your website traffic suddenly spikes dramatically you should immediately perform a source code scan and verify that you have not been hacked. Hacked sites frequently see a dramatic spike in traffic. Of course if you just published some advertising it could be as a result of that too, so don’t become alarmed every time you see a spike.
One cause of a traffic spike may be that your site is being included in a spamvertizing campaign. A hacker will send out spam and include a link to your site which either hosts malware or redirects traffic to another malicious site. Hackers do this to avoid spam detection. Your site is a “clean” domain and is not known to host malware when it is first infected. By including a link to your site instead of their own known malware hosting site, hackers avoid spam detection. This results in a dramatic spike in your site traffic.
In addition to JavaScript based traffic monitoring tools like Google Analytics, you should also monitor your site traffic for “bot” traffic which is not usually logged by Google Analytics. You can use Wordfence’s live traffic feature or another server-based traffic monitoring tool. Your hosting provider may provide charts that show server traffic or bandwidth usage.
Visit your own website regularly
As a routine, simply visit a few pages on your own site as a sanity check at least once a day. If you understand HTML then also take a quick look at the source code of the page to make sure that no malicious JavaScript has suddenly appeared.
If you notice any changes or any strange text injected into your pages, you should immediately perform a scan on your site to check for an infection. PHP errors are also a common sign that you may be infected and these often appear at the very top of your page, often above the content.
Check Google and Bing search results
At least once a day you should enter the following search string into Google and Bing to see what they have indexed, and what’s being cached. Just be sure you don’t include a space after site: otherwise you won’t get the results you are expecting.
site:www.yourwebsite.com
Japanese keyword hack
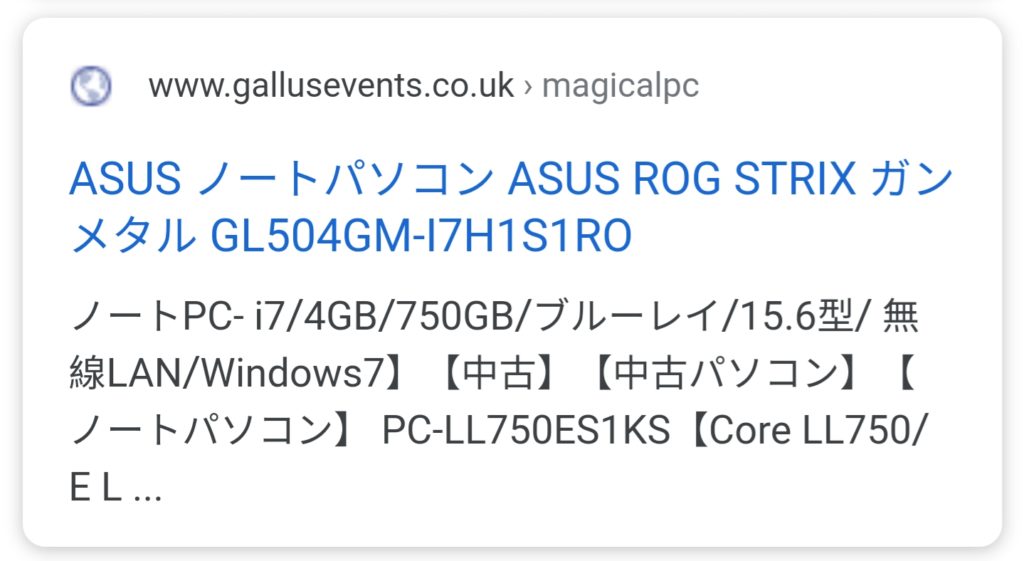
The type of hack shown at the right creates autogenerated Japanese text to your site we call that kind of hack the “Japanese keyword hack”.
The Japanese keywords hack typically creates new permalinks with automatically generated Japanese text on your site in randomly generated directory names (for instance, . The pages usually don’t really exist, they’re a bit of code that’s inserted in key points of the WordPress core code and generate pages in much the same way as WordPress does itself. These pages are monetized using affiliate links to stores selling fake brand merchandise and then shown in Google search.
Typically, when you click one of those links that now appear in Google search, you will either be redirected to another site, or you will see a page full of gibberish content. However, you might also see a message suggesting that the page does not exist (for example, a 404 error). Don’t get hoodwinked! Hackers will try to make you believe the page was removed or fixed when it’s still hacked. They do this by cloaking the content, often so it only appears if you are accessing the site from a specific geographic location.
Get Virtco Threat Report
[pt_view id=”1e954a46xk”]